Solutions
Learn how Stixify helps teams operationalise threat intelligence extraction, improve detection and hunting, reduce manual research, strengthen intelligence graphs, and support AI-ready workflows.
Overview
Solution pages explain the broader outcomes Stixify helps teams achieve.
If use-case pages show how individual workflows work, solution pages show why those workflows matter across a team, a programme, or a wider security stack.
Explore solutions
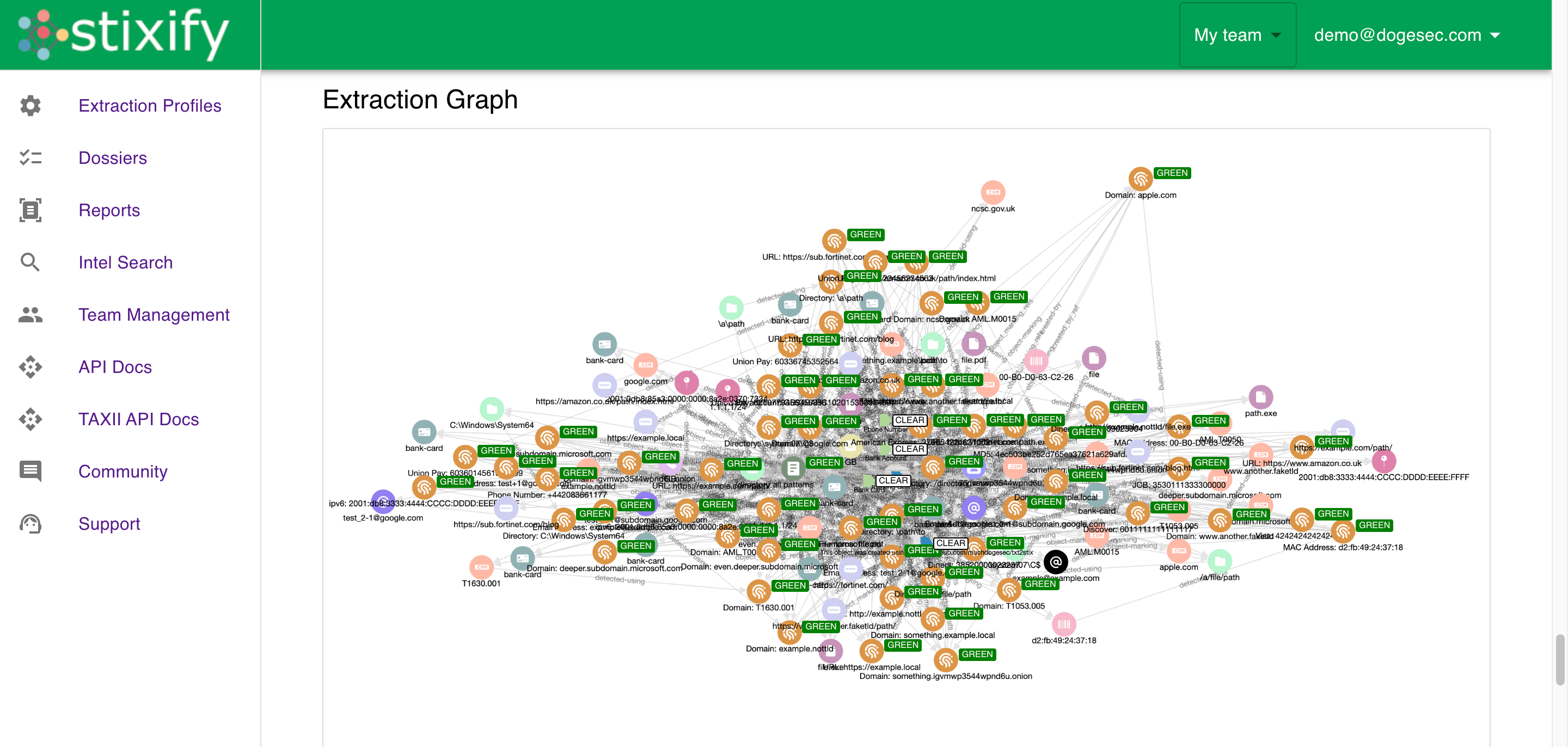
- Operationalise Threat Intelligence Extraction: Turn unstructured reports into structured intelligence that can be searched, shared, and acted on.
- Improve Detection and Hunting with Structured Threat Intelligence: Use ATT&CK-aligned behaviours, Attack Flow context, and linked intelligence to strengthen defensive workflows.
- Reduce Manual CTI Extraction and Enrichment: Help analysts spend less time extracting and cross-referencing and more time using intelligence.
- Build a More Connected Intelligence Graph: Add structured intelligence from reports into existing TIPs, graph stores, and CTI platforms.
- Scale Security Workflows with AI-Ready Threat Intelligence: Support integrations, automation, and AI agents with structured data instead of raw reports.
Looking for hands-on workflows instead?
If you want the task-level view, explore the Use Cases pages.
