Enrich IoCs and TTPs from Unstructured Reporting
Use Stixify to extract and connect observables, techniques, and related context from reports so analysts can enrich investigations and pivot faster.
Overview
An indicator or technique on its own is rarely enough. An IP address, domain, hash, malware family, or ATT&CK technique only becomes useful when you can quickly understand where else it appears, what it connects to, and how it fits into the wider threat picture.
That is the core value of enrichment. Defenders do not just need more data. They need faster ways to add context to the data they already have.
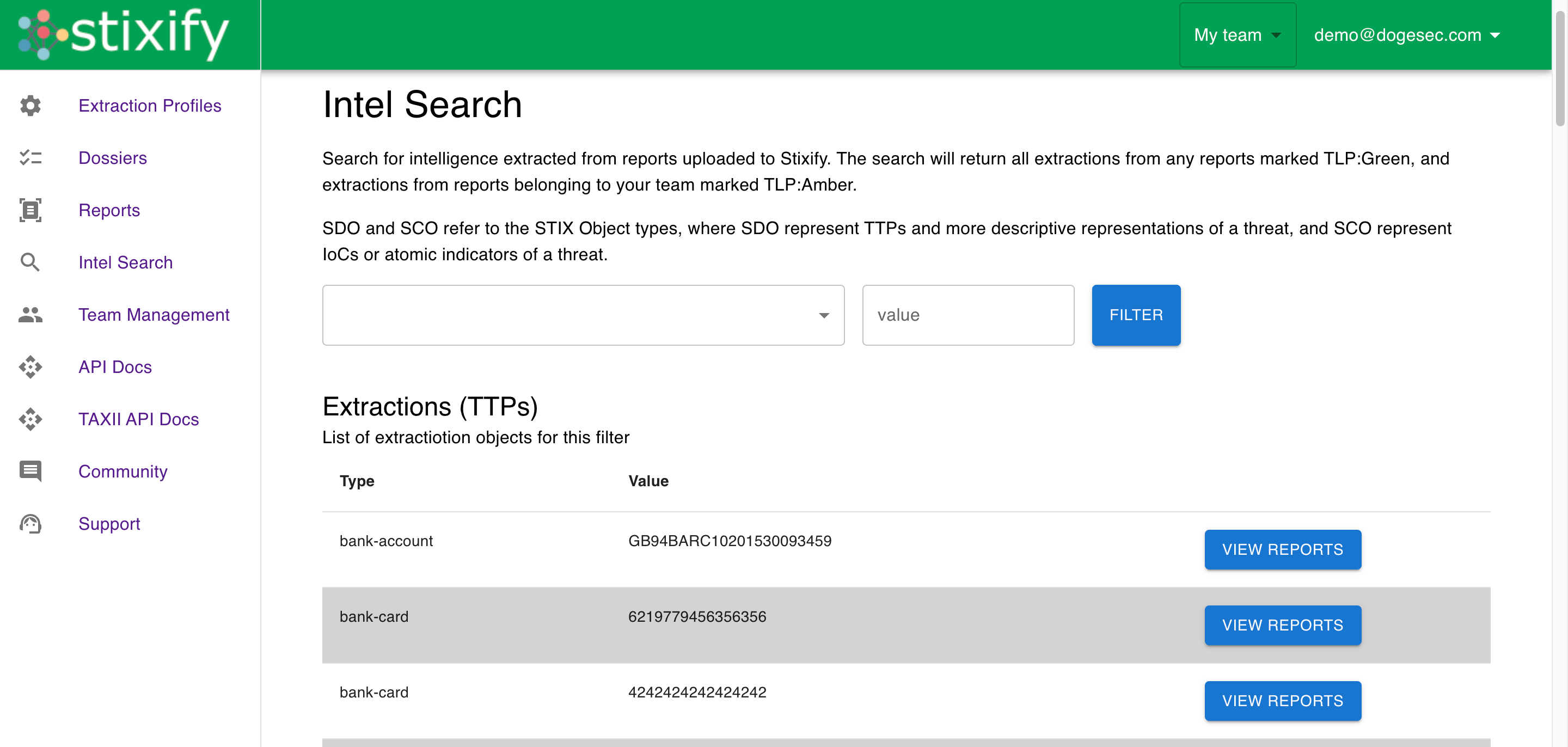
Stixify helps by turning unstructured reporting into structured threat intelligence that can be searched, pivoted on, and moved into other systems. Analysts can start with an IoC or TTP, find related reporting discussing the same thing, and use those relationships to build a richer view of the activity they are investigating.
What this solves
Most teams already collect IoCs and TTPs from many places. The challenge is not getting the first data point. The challenge is enriching it quickly enough to make it useful.
Common problems include:
- an analyst has an IoC, but needs to know which reports mention it
- a team sees a technique internally, but needs more context on where else it has been observed
- related reporting exists, but it is time-consuming to find and compare manually
- valuable external intelligence stays isolated from the internal tools where analysts already work
- existing intel graphs remain incomplete because report intelligence is not being added in a structured way
Stixify addresses these issues by making extracted report intelligence searchable and portable.
Start with an IoC or TTP and work outward
One of the most useful enrichment workflows begins with a single object.
That object might be an IP address from an alert, a domain from a phishing investigation, a malware family from a sandbox run, or an ATT&CK technique seen during hunting. On its own, that starting point often tells you very little. The next question is always the same: where else does this appear, and what else is connected to it?
Stixify makes that question easier to answer.
Because report content is converted into structured STIX 2.1 objects, analysts can look up extracted IoCs and TTPs directly and pivot from them into the reports and related intelligence where they appear. That changes enrichment from a manual reading exercise into a structured search workflow.
Find related reporting and connected context
Reports are often more useful together than on their own.
Different researchers may describe the same infrastructure, malware family, intrusion set, or technique chain from different angles. One report may provide deeper observables, another may offer ATT&CK context, and another may add timeline or campaign detail.
Stixify helps teams move from one object into that wider context more efficiently. This matters because enrichment is often about confidence as much as detail. Seeing the same infrastructure or behaviour appear across more than one source can strengthen triage decisions and help analysts judge whether the finding is isolated or part of something broader.
That can support workflows such as:
- validating whether an observable is widely referenced
- connecting one technique to a broader set of related behaviours
- comparing how different reports describe the same activity
- building more complete context around an alert, case, or hunting lead
Improve the quality of analysis
The value of enrichment is not limited to collecting more references. Good enrichment improves the quality of analysis.
When teams can look up an IoC or TTP and immediately see related reporting, they gain a better basis for interpretation. They can distinguish between one-off artifacts and recurring patterns. They can see whether a technique is appearing as part of a wider intrusion path. They can identify whether the same malware family is linked to different infrastructure over time.
This supports better analyst workflows:
- triage becomes more informed because suspicious artifacts can be checked against known reporting quickly
- investigations move faster because analysts can pivot to related context without rebuilding it manually
- threat hunting improves because one technique or object can be expanded into a fuller set of associated behaviours
- CTI production becomes easier because supporting references and connections are already available
Push enriched data into the rest of the stack
Enrichment becomes much more powerful when it does not stop inside one product.
Stixify stores extracted intelligence as structured STIX 2.1 objects and supports workflows that make it easier to move that intelligence into the tools your team already relies on. That includes TIPs, CTI repositories, internal graph stores, TAXII consumers, and other systems designed to operationalise threat intelligence.
This is where enrichment stops being a point-in-time analyst task and starts becoming part of the organisation’s wider intelligence capability.
Explore next
- Want the broader outcome this supports? See Build a More Connected Intelligence Graph.
- Want to use enriched techniques for defensive coverage and emulation? See Map Reports to MITRE ATT&CK and Attack Flow.
- Want to push enriched data into other platforms and automations? See Integrate Stixify into Your Security Stack and AI Workflows.
