Scale Security Workflows with AI-Ready Threat Intelligence
Support integrations, automation, and AI agents with structured intelligence from Stixify instead of forcing downstream systems to interpret raw reports.
Overview
Security workflows become easier to scale when external intelligence is available as structured data instead of raw documents. That matters for classic integrations, internal automation, and newer AI-driven workflows alike.
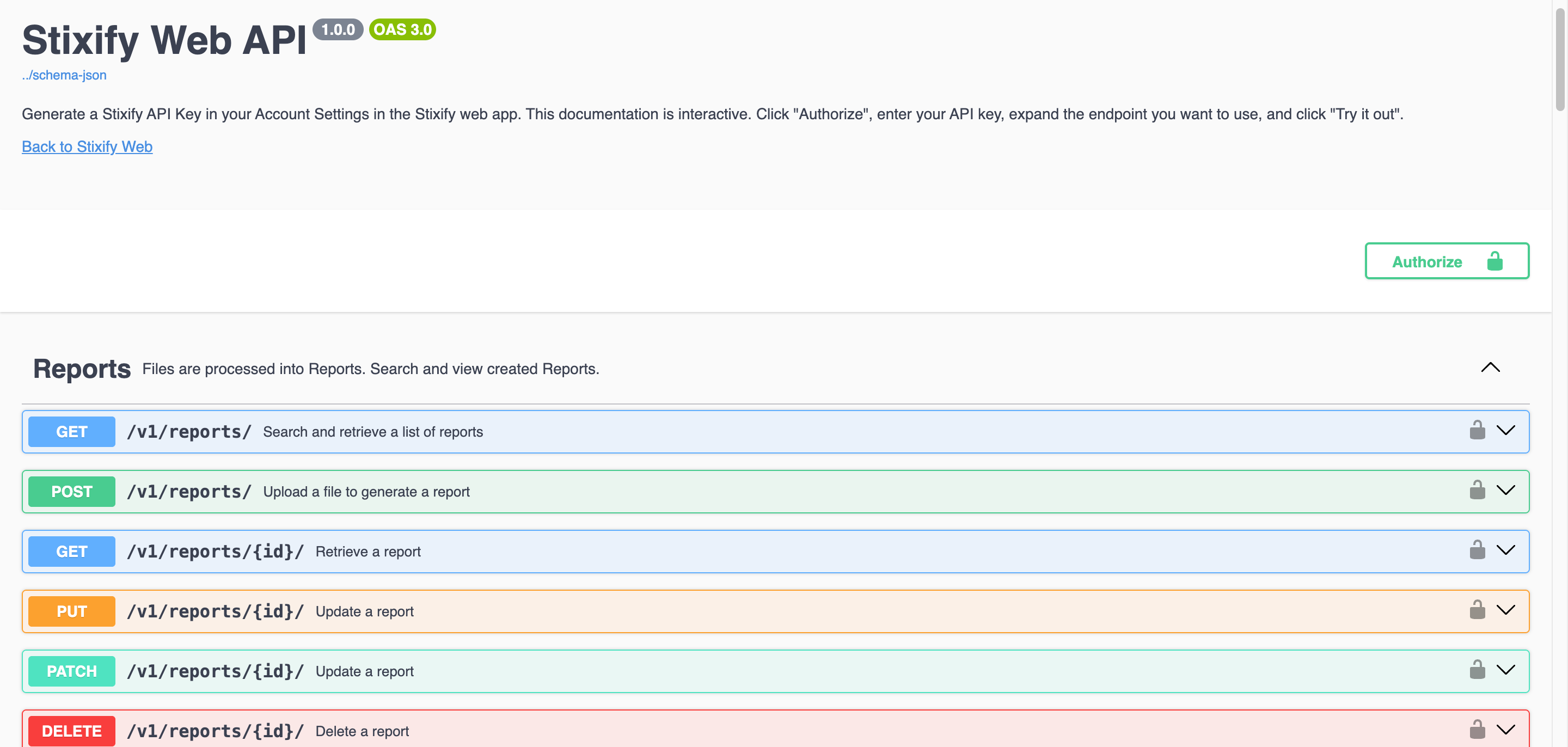
Stixify helps by turning reports into structured intelligence that can be retrieved through APIs, exported as STIX bundles, and shared into systems that need clean, machine-readable CTI inputs.
The value here is not only interoperability. It is input quality. Downstream systems work better when they do not have to interpret long-form reports on their own before they can do anything useful.
What this outcome looks like
Scaling workflows with AI-ready threat intelligence means:
- giving automations a structured source of threat data
- making it easier to enrich cases, alerts, and investigations automatically
- helping AI agents retrieve linked CTI instead of scraping raw reports
- moving structured report intelligence into tools that already support STIX workflows
- creating repeatable integrations instead of one-off manual processes
This is useful for both established security engineering workflows and newer AI-assisted ones.
Why this matters
Automation and AI are most useful when the inputs are reliable.
When systems have to work directly from long-form reports, results are slower and less predictable. Structured threat intelligence gives them a cleaner starting point and preserves more analytical context than flat text extraction alone.
That matters because many downstream workflows are not trying to replace human analysis. They are trying to:
- enrich a case automatically
- give an analyst faster context
- correlate one artifact with related intelligence
- provide an agent with a clean retrieval layer
All of those become easier when the upstream intelligence is structured well.
Support classic automation and custom integrations
Long before AI became part of the workflow, teams were already trying to automate enrichment, case support, and intelligence movement between systems.
Stixify supports those older but still critical workflows by exposing structured intelligence through usable integration surfaces. That makes it easier to:
- build internal services around extracted IoCs and TTPs
- feed structured intelligence into case or alert enrichment pipelines
- standardise how report-derived intelligence enters downstream tools
- reduce repeated manual handoffs between analysis and engineering systems
This makes Stixify useful not only for analysts, but also for the teams responsible for workflow reliability and scale.
Why AI-ready matters specifically
AI agents are far more useful when they can retrieve structured intelligence instead of attempting to infer everything from raw documents.
For Stixify, AI-readiness does not mean inventing intelligence. It means making extracted intelligence available in a cleaner form:
- structured objects instead of long narrative blobs
- linked context instead of isolated data points
- queryable data instead of scattered attachments
- exportable outputs instead of manual copy-and-paste
That gives agent workflows a stronger foundation for retrieval, summarisation, enrichment, and decision support.
Where Stixify fits
Stixify fits as the structured-intelligence layer between unstructured source material and the wider security stack.
That can support:
- internal enrichment services
- case and incident automation
- TAXII-based sharing workflows
- STIX bundle export into CTI platforms
- AI agents that need machine-readable threat data
In each case, the pattern is the same: reports are turned into intelligence that other systems can actually use.
