Operationalise Threat Intelligence Extraction
Turn unstructured reports, PDFs, documents, and web pages into structured intelligence that can be monitored, searched, enriched, shared, and acted on across your security workflows.
Overview
Threat reporting is valuable, but it often arrives in the least operational format possible. Important details are spread across PDFs, Word documents, slides, web pages, and other narrative formats that still need to be read, interpreted, and restructured before they can support action.
That creates a familiar gap for security teams. They have access to useful reports, but not always in a form they can use quickly. Analysts end up extracting indicators by hand, copying techniques into notes, rebuilding relationships between objects, and moving context into other systems one step at a time.
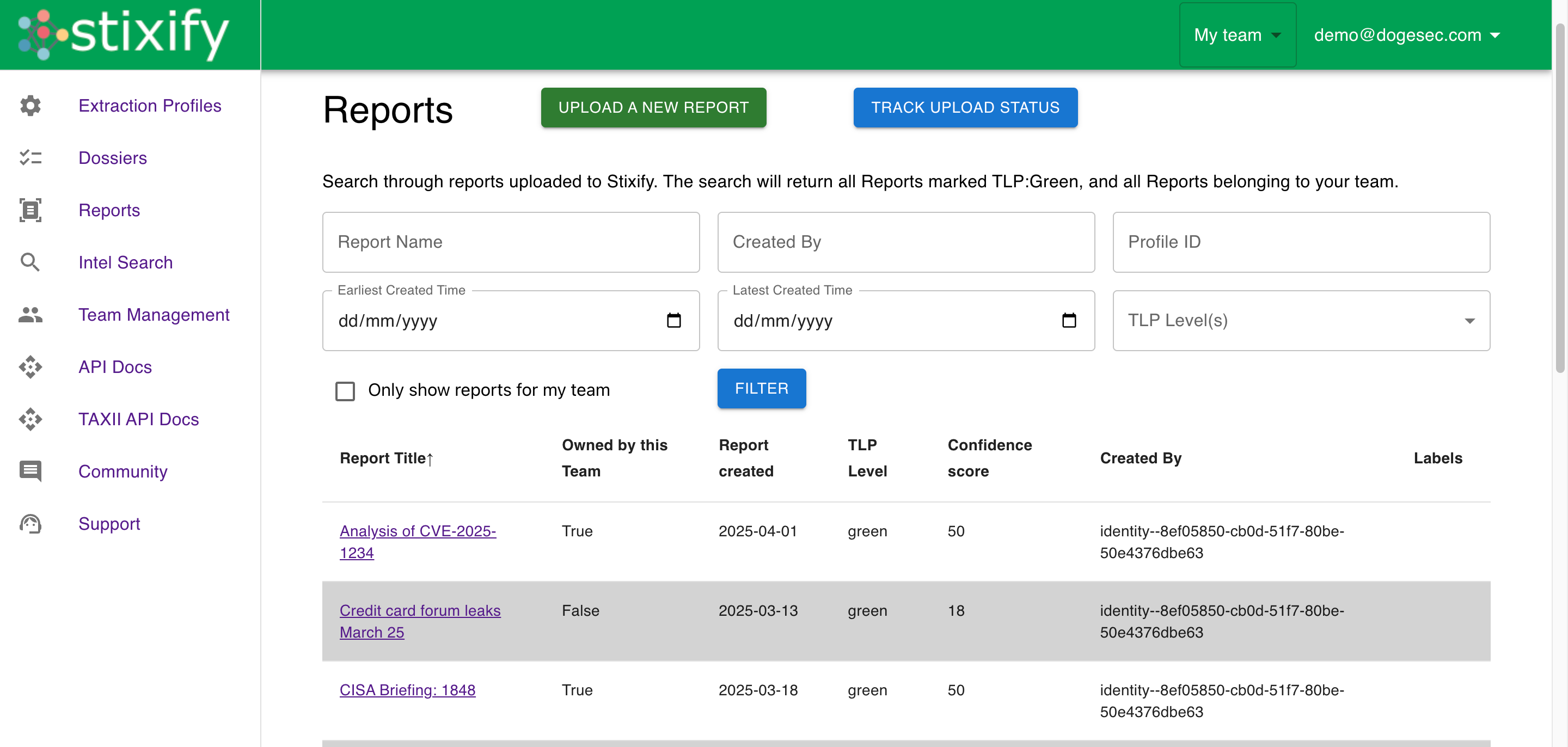
Stixify helps close that gap. It turns unstructured source material into structured threat intelligence that can be searched directly, enriched through pivots and correlation, and shared into the rest of the security stack.
The result is not just faster document processing. It is a better way to make reporting operational.
What this outcome looks like
Operationalising threat intelligence extraction means making reports part of the working environment instead of leaving them as attachments and reading queues.
In practice, that means:
- extracting IoCs, TTPs, and relationships into structured intelligence
- searching and pivoting across connected reports instead of isolated documents
- mapping reporting to ATT&CK and behavioural context
- moving intelligence into downstream platforms and workflows
- giving CTI, SOC, hunting, and detection teams a more usable source of external context
The benefit is not just efficiency. It is consistency. Teams can work from the same structured intelligence layer instead of rebuilding context from scratch each time a report matters.
Why this matters
Unstructured reports often contain some of the best detail about current adversary behaviour, infrastructure, and campaigns. But that value drops quickly if every report has to be processed manually before it can support a hunt, an investigation, or an enrichment workflow.
When that process stays manual:
- useful details are easier to miss
- analysts spend time on repetitive extraction work
- relationships between observables and behaviours are harder to preserve
- external context is harder to compare with internal findings
- downstream teams receive less usable output
Operationalising extraction solves that by making reporting more searchable, more structured, and easier to distribute across a wider workflow.
From document intake to working intelligence
The core change here is simple: a report stops being only something to read and becomes something the rest of the stack can use.
That matters because most security workflows benefit from structure:
- analysts need structured pivots when investigating
- CTI teams need reusable outputs instead of copied notes
- defenders need ATT&CK-aligned behaviours they can compare with real coverage
- engineers need machine-readable data for integration and automation
Stixify supports that transition by turning a document-processing step into an intelligence-production step.
Where Stixify fits
Stixify helps teams move from passive reading to active use.
It supports the path from unstructured content to structured STIX 2.1 intelligence to downstream use. That means teams can start with a report, identify what matters, pivot into related intelligence, and push the result into the workflows that need it next.
This supports a wide range of teams:
- CTI teams that need faster access to usable intelligence
- SOC teams that need context during triage and investigation
- threat hunters who need structured behaviour and related reporting
- detection engineers who need current external tradecraft to work from
- security engineering teams building integrations, automations, or internal tooling
What makes this a solution, not just a feature
The value is not any one capability in isolation. It is the way the pieces fit together:
- document and page ingestion creates a repeatable starting point
- structured extraction makes reporting easier to search and use
- ATT&CK and Attack Flow context add defensive relevance
- search and dossiers help teams reuse the intelligence later
- export and integration make the intelligence available outside the platform
That combination is what turns report handling into a working intelligence capability.
A better foundation for everything downstream
Many of the higher-value workflows teams want later depend on getting this first step right.
If extraction is inconsistent, then enrichment is weaker. If relationships are lost, graph building is weaker. If the output is not structured, integrations and automations are weaker. If ATT&CK and behavioural context are missing, detection and hunting workflows lose value.
That is why this solution sits near the top of the Stixify story. Better extraction does not only save time. It improves the quality of everything that happens after.
