Accelerate Threat Research and Investigation
Use Stixify to cross-reference reports faster, surface related intelligence, and keep investigations moving without repeated manual extraction work.
Overview
Threat research and investigation often slow down for a simple reason: too much time is spent moving between disconnected reports, tabs, notes, and search queries just to assemble basic context.
Analysts already know how to investigate. The friction comes from the mechanics. Finding the right report, checking whether a behaviour has shown up elsewhere, comparing related writeups, keeping track of useful findings, and spotting broader patterns across many documents all take time when reporting is scattered and unstructured.
Stixify helps reduce that overhead. It structures the intelligence inside each report and gives analysts faster ways to cross-reference, search, group, and return to what matters.
The result is not just faster reading. It is a more efficient research workflow.
What this solves
Research and investigation workflows usually break down in familiar ways:
- analysts need to cross-reference entities, techniques, malware, or infrastructure across many reports
- similar activity may be described in multiple places, but the links are hard to identify quickly
- useful reports get lost because there is no clean way to save and revisit them
- trend analysis requires repeated manual review of large volumes of material
- valuable context is available, but it takes too long to collect and compare
Stixify addresses these problems by making reports easier to search, easier to connect, and easier to reuse during ongoing work.
Cross-reference faster
A large part of threat research is cross-referencing.
An analyst may start with one report, one malware family, one ATT&CK technique, one domain, or one threat actor. Very quickly the question becomes: where else does this show up, and what is related to it?
Without structure, that means searching manually across many documents, repeating the same lookups, and trying to remember which reports were already reviewed. With Stixify, analysts can work from extracted data and connected reporting instead.
This helps teams:
- search for specific IoCs, TTPs, malware families, or other extracted objects
- pivot from one report into others that reference the same or similar activity
- compare how multiple sources describe the same behaviour
- build context around a case without leaving the platform repeatedly
- reduce the time spent doing repetitive source-by-source searches
Search for patterns across reporting
Threat research is not only about individual reports. It is also about patterns.
Analysts often want to know whether a behaviour is becoming more common, whether a malware family is appearing across more sources, or whether several reports are beginning to cluster around the same topic. These patterns are hard to spot when reporting is reviewed one document at a time.
Stixify helps by making it easier to search across many reports and identify patterns in the underlying intelligence. That is useful for:
- spotting recurring techniques across recent reporting
- tracking how a malware family or intrusion theme is evolving
- identifying repeated infrastructure or behaviour across separate writeups
- understanding which themes are becoming more prominent over time
Keep track of important findings
Research work is rarely linear. Analysts often move between several threads at once, pause and return to a case later, or save material for deeper review by another teammate.
That makes simple workflow features surprisingly important. If useful pages and dossiers cannot be saved and revisited easily, time gets wasted rediscovering the same material.
Stixify helps by giving analysts a clearer way to preserve important context across ongoing work. That supports practical day-to-day workflows such as:
- saving high-value reports for later analysis
- keeping track of documents relevant to an active investigation
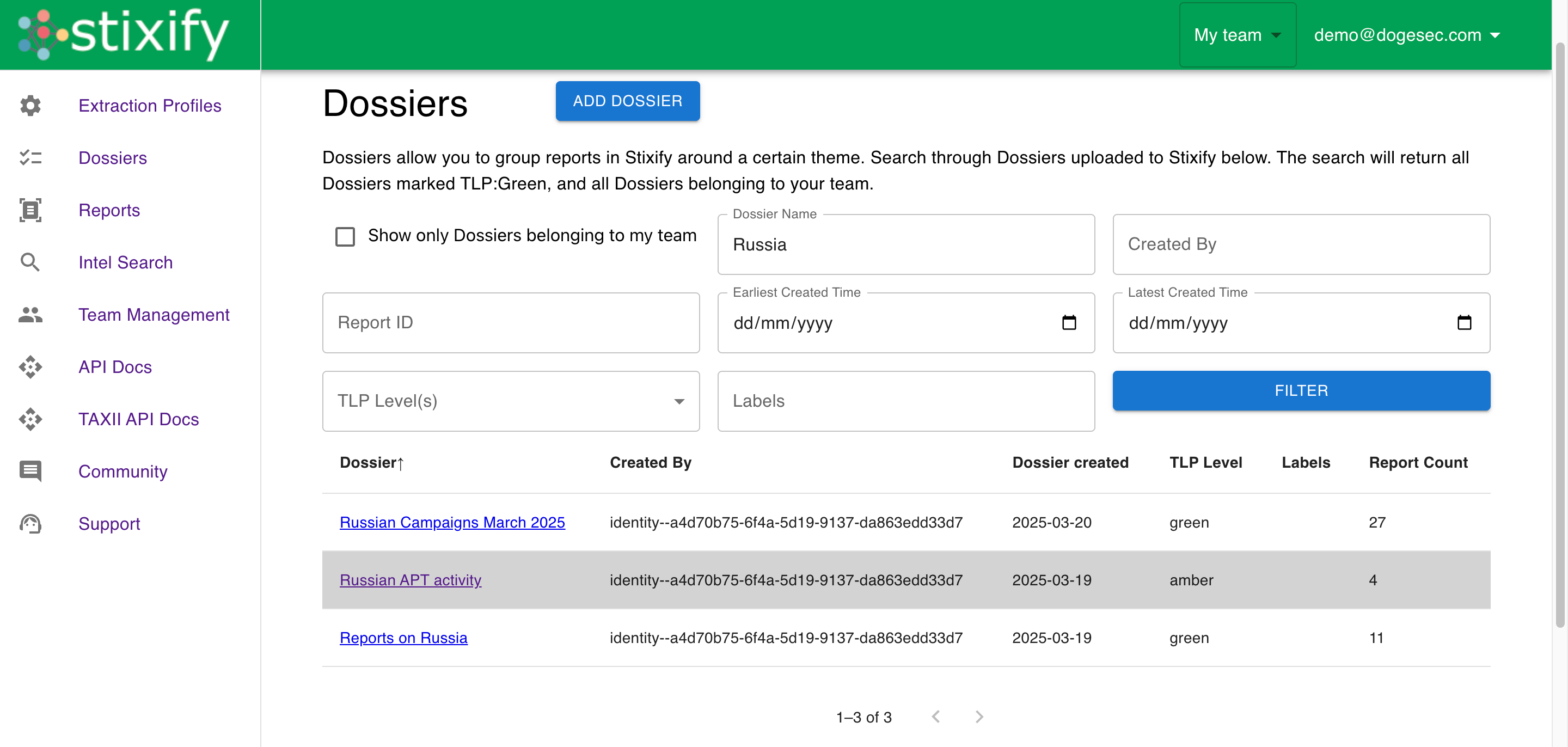
- grouping work into dossiers or themed research threads
- returning quickly to important context without rerunning searches
- maintaining continuity across multi-day research efforts
Support better investigations, not just faster searches
Speed matters, but the goal is not to help analysts click through more content. The goal is to help them investigate more effectively.
Stixify supports that by combining searchable report intelligence, extracted objects, linked context, and reusable groupings in one workflow. Together, these reduce friction across the full research process and make it easier to move from an initial lead to a broader, better-supported assessment.
Explore next
- Want the broader outcome this supports? See Reduce Manual CTI Extraction and Enrichment.
- Want to focus more on extracting usable intelligence from source material first? See Extract Threat Intelligence from Unstructured Documents.
- Want to analyse recurring adversary behaviour through ATT&CK and Attack Flow outputs? See Map Reports to MITRE ATT&CK and Attack Flow.
