Improve Detection and Hunting with Structured Threat Intelligence
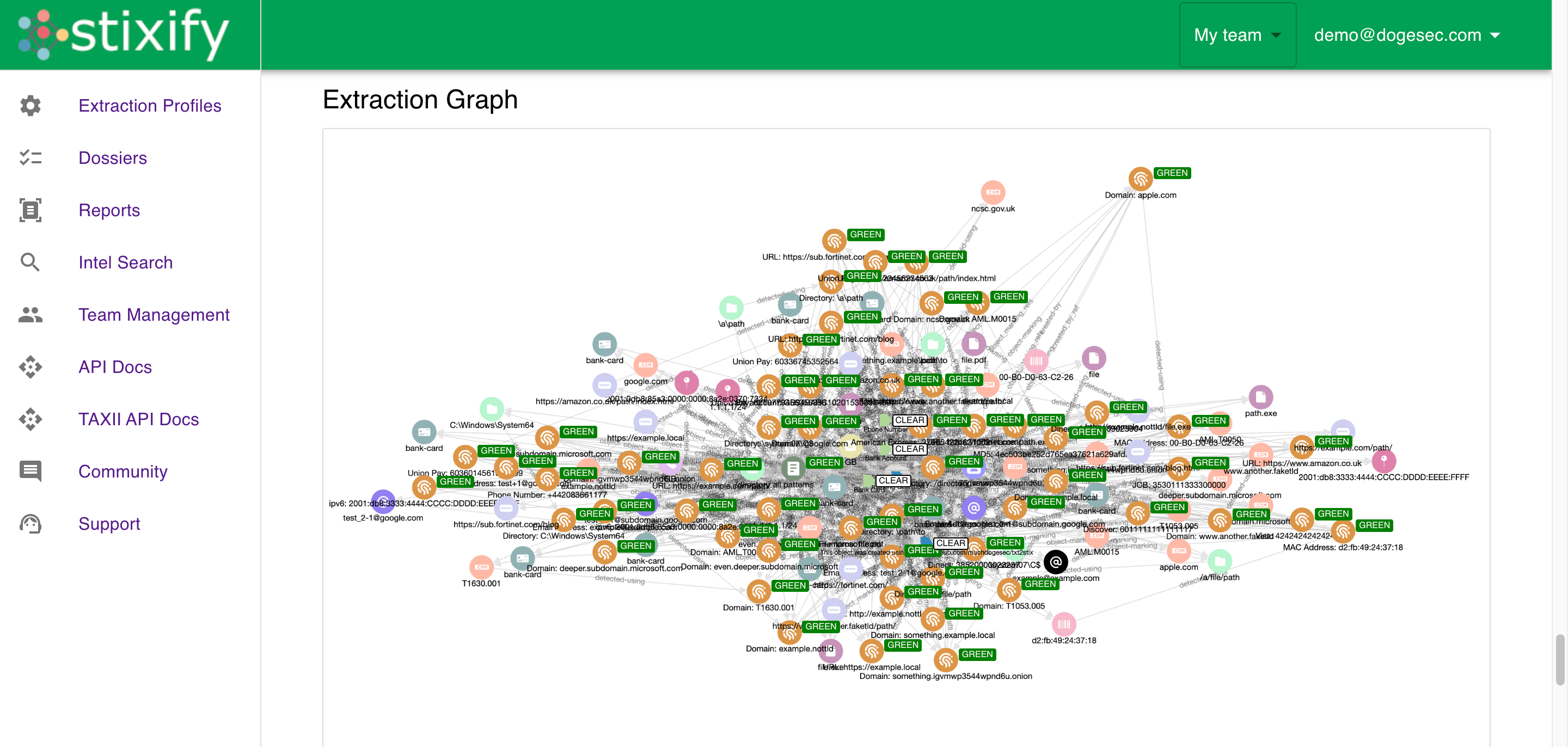
Use ATT&CK-aligned techniques, Attack Flow context, and linked report intelligence from Stixify to strengthen detection engineering, hunting, and triage workflows.
Overview
Detection and hunting workflows improve when defenders can work from real observed behaviour instead of isolated indicators or abstract framework references.
Threat reports often contain exactly that behaviour, but they are hard to use directly. Techniques are embedded in narrative text, attack progression has to be reconstructed manually, and related reporting is difficult to compare at speed.
Stixify helps turn that into a stronger defensive workflow. It maps reporting to MITRE ATT&CK, preserves adversary behaviour through Attack Flow style outputs, and makes it easier to correlate related activity across reports.
This is not only about classification. It is about giving defenders a more practical way to use external tradecraft in operational workflows.
What this outcome looks like
Improving detection and hunting with structured threat intelligence means defenders can:
- search for current tradecraft by ATT&CK technique
- understand how techniques fit together in a broader intrusion path
- use report-derived behaviour to guide hunts and detection improvements
- compare external behaviour with internal telemetry and coverage
- move from one observed behaviour to related reports, patterns, and context
This is more useful than simply collecting more indicators. It helps teams think in terms of attacker behaviour and defensive visibility.
Why this matters
Defenders often know the framework they want to use. The challenge is grounding it in current, usable intelligence.
Without structure:
- ATT&CK references stay high level
- hunting starts from incomplete context
- coverage reviews are harder to tie to recent observed activity
- emulation planning takes more manual preparation
- techniques are discussed, but not always operationalised
Structured report intelligence makes those workflows more practical by turning narrative content into something that can be searched, compared, and reused.
Use ATT&CK as a working pivot
MITRE ATT&CK becomes much more useful when it is a pivot point rather than a label.
In practical terms, a defender might start with one technique seen in a hunt hypothesis, a triage case, an internal alert, or a coverage review. The next step is usually to understand where else that technique appears, how it is being used in the wild, and what related behaviours surround it.
Stixify supports that by making ATT&CK-aligned report intelligence easier to search and compare. That helps teams:
- review reports that reference the same technique
- compare how different sources describe similar tradecraft
- identify which behaviours appear together repeatedly
- use external reporting to prioritise coverage discussions
This turns ATT&CK from a documentation framework into a more active research and defensive input.
Why Attack Flow context matters
Technique extraction on its own is useful, but often incomplete.
A list of techniques can tell defenders what happened. It does not always explain how those behaviours fit together. Attack-flow style context is valuable because it preserves more of the sequence and relationship between attacker actions.
That matters for defensive work because:
- hunting becomes easier when analysts can reason about adjacent behaviours
- detection engineering improves when teams understand likely progression
- investigation workflows gain more context around what to look for next
- emulation planning can be based on behaviour chains instead of disconnected technique IDs
This is one of the clearest differences between basic ATT&CK tagging and more operational behavioural modelling.
Support coverage reviews and hunt planning
External reporting is often one of the best places to validate whether current coverage reflects current tradecraft.
Stixify helps make that validation more practical. Instead of reading reports one by one and translating them manually into hunt notes or coverage gaps, teams can work from structured ATT&CK-aligned data and Attack Flow context.
That supports questions such as:
- which techniques are showing up often enough to justify detection work?
- which behaviours appear together in ways that current playbooks do not reflect?
- where is external reporting pointing to tradecraft that internal coverage may miss?
- how should recent adversary behaviour influence hunt prioritisation?
This makes public reporting easier to use as a real defensive planning input instead of a background reference.
Where Stixify fits
Stixify fits well where teams want to use external reporting as a real defensive input instead of background reading.
It helps bridge the gap between narrative reporting and working defensive artefacts by combining:
- ATT&CK-aligned technique extraction
- Attack Flow style behavioural context
- linked IoCs and related report entities
- standards-based export and integration paths
That makes it useful not just for CTI teams, but also for the defender workflows that rely on current behaviour data.
