Integrate Stixify into Your Security Stack and AI Workflows
Use the Stixify REST API, TAXII API, and STIX bundle export paths to power custom integrations, enrich existing tools, support AI agents, and move report-derived intelligence into detection and response workflows.
Overview
Report-derived intelligence is much more useful when it can move into the tools your team already uses.
That is where the Stixify integration surfaces help. They make it possible to take structured intelligence extracted from unstructured reporting and use it in custom tooling, existing CTI platforms, internal automations, and AI-driven workflows.
The goal is simple: do not leave useful intelligence trapped in a document viewer.
What this solves
Without integration, useful external intelligence often gets stuck in manual workflows:
- analysts read reports, but the extracted intelligence never reaches the systems where the team actually works
- enrichment stays manual instead of becoming part of a repeatable workflow
- detection, hunting, and triage processes miss useful report-derived context because it is not available in the right place
- internal tools and automations have no clean way to pull in structured threat data
- AI agents are forced to work from raw documents instead of structured intelligence
Stixify helps solve this by exposing intelligence through interfaces other systems can consume.
Build custom integrations and tooling
Every team works differently. Some rely on a TIP, some use internal analyst tools, and some build lightweight services around their existing stack.
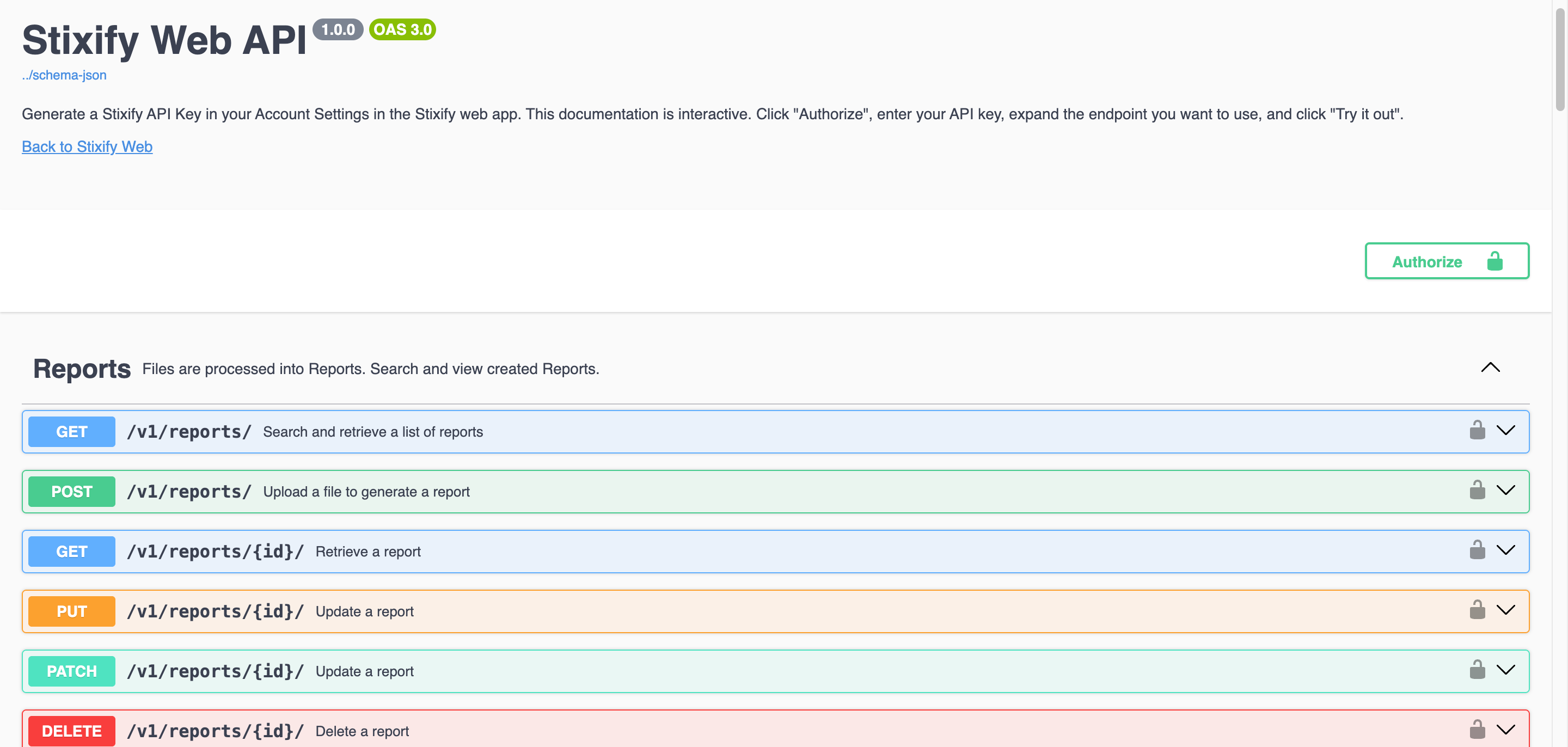
The Stixify REST API makes that possible. Teams can build custom integrations to:
- pull structured report intelligence into internal tools or dashboards
- create enrichment services around IoCs, TTPs, and related reports
- surface report intelligence inside case, incident, or research workflows
- correlate external reporting with internal findings
- automate repetitive analyst tasks
This makes Stixify easier to fit into the workflow you already have rather than forcing a new one.
Use standards-based sharing and export
Not every integration needs custom code.
For teams that already support STIX and TAXII workflows, the Stixify TAXII API and STIX bundle export paths offer more standard ways to move intelligence into existing platforms. This is useful when report-derived intelligence needs to sit alongside other CTI sources without building a bespoke connector for everything.
That can support workflows such as:
- exporting structured report intelligence into a CTI platform
- feeding a TAXII-capable environment with derived intelligence
- preserving portable STIX outputs for later batch import or sharing
Integrate Stixify with OpenCTI
Stixify also has a dedicated OpenCTI connector for teams using OpenCTI as a central CTI platform.
According to the connector documentation, the integration synchronizes intelligence from Stixify Dossiers into OpenCTI so teams can ingest structured STIX data extracted from reports on a schedule. The connector uses a Stixify API key plus one or more dossier IDs and imports both historical and incremental updates.
This is especially useful for organisations that already use OpenCTI as their working intelligence graph and want report-derived intelligence to flow into that environment without building their own ingestion layer first.
Enrich downstream detection and response workflows
Public intelligence is most valuable when it influences action.
Stixify can support downstream detection and response workflows by making extracted intelligence easier to use in the systems responsible for triage, hunting, detection engineering, and response. Structured IoCs, TTPs, relationships, and ATT&CK-aligned behaviour are much easier to operationalise than raw text.
That can support workflows such as:
- enriching alerts or cases with related report intelligence
- giving analysts more context during triage and incident review
- feeding threat hunting workflows with current external behaviours and observables
- supporting detection engineering with recently observed techniques and activity patterns
Support AI agents with structured intelligence
Stixify is also a strong fit for AI-agent workflows.
AI agents are much more useful when they can retrieve structured intelligence instead of trying to interpret large volumes of raw documents on their own. Stixify gives them a cleaner input layer: extracted objects, linked intelligence, and data that can be queried or exported in machine-readable form.
That can support use cases such as:
- enriching a case automatically with related report intelligence
- looking up an IoC or TTP and returning connected context
- summarising related reporting across a dossier or investigation thread
- supporting analyst copilots that need reliable CTI inputs
Where this fits in the stack
Stixify fits anywhere report-derived intelligence needs to move into a working system.
For CTI teams, that may mean feeding a TIP or graph. For SOC teams, it may mean enriching cases or supporting triage and hunting. For engineering teams, it may mean building custom services around extracted intelligence. For organisations investing in AI, it may mean giving agents access to structured CTI instead of leaving them to parse raw reports.
The common theme is the same: reports become much more valuable when the resulting intelligence can be searched, enriched, shared, and acted on outside the document itself.
Explore next
- Want the broader outcome view? See Scale Security Workflows with AI-Ready Threat Intelligence.
- Want to see the integration surfaces directly? See Integrations.
- Want the specific connector path into OpenCTI? See OpenCTI Integration.
- Want to use ATT&CK and behaviour data in defensive workflows? See Map Reports to MITRE ATT&CK and Attack Flow.
