Map Reports to MITRE ATT&CK and Attack Flow
Use Stixify to turn narrative report content into ATT&CK-aligned techniques and Attack Flow outputs that are easier to use in hunting, detection, and emulation workflows.
Overview
Threat reports often describe adversary behaviour in rich detail, but that detail is harder to use operationally when it stays trapped in prose. Teams need a way to move from narrative reporting to ATT&CK-aligned techniques and ordered behavioural context.
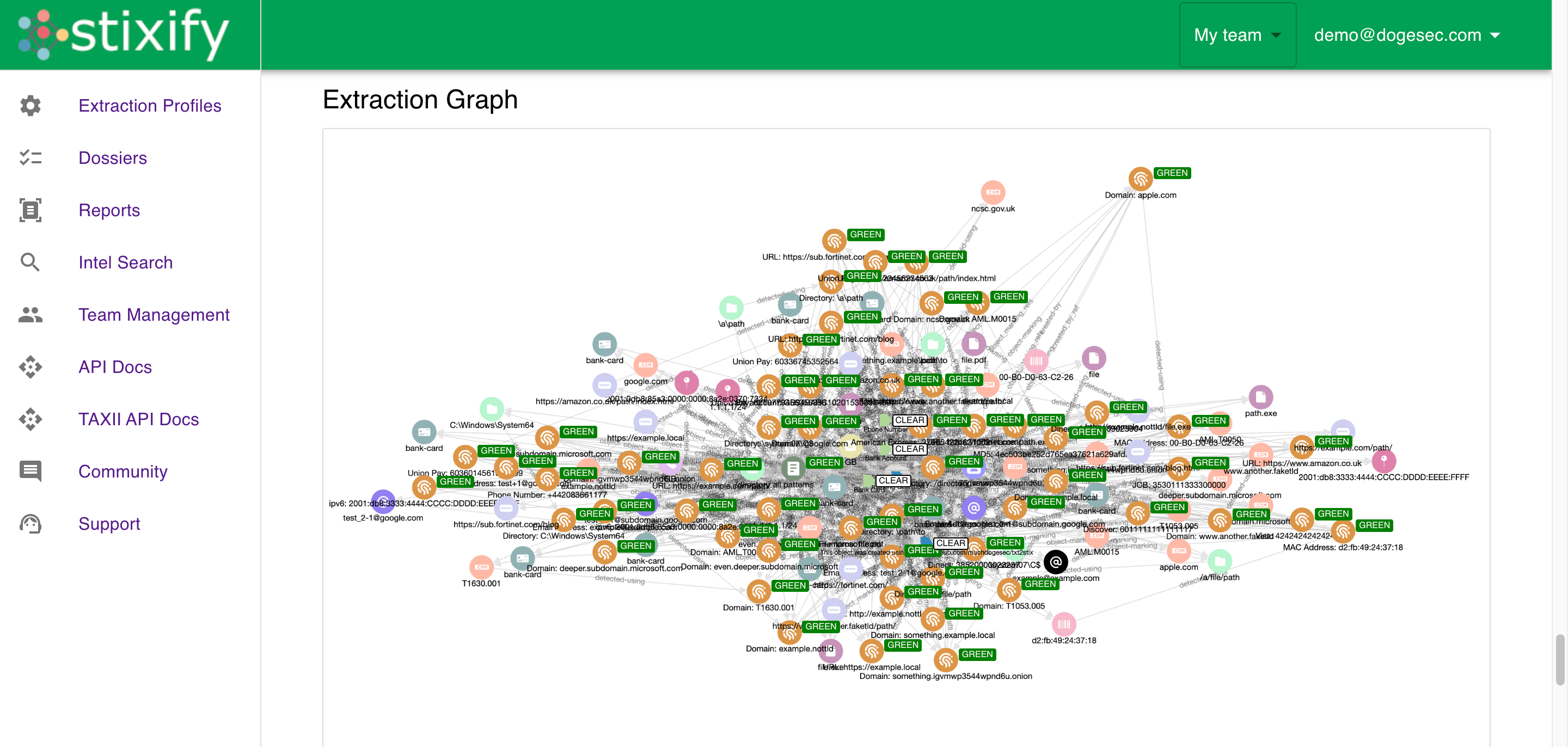
Stixify helps close that gap by extracting structured intelligence, aligning techniques to MITRE ATT&CK, and representing adversary behaviour in a form that is easier to search, compare, and use in downstream workflows.
This is useful for teams that already use ATT&CK heavily, but also for teams that want a better way to connect reporting to detection, hunting, and emulation work.
What this solves
Without structured ATT&CK and behaviour mapping:
- technique references are harder to search consistently
- analysts lose time pulling ATT&CK context out of reports
- defensive teams work from isolated labels instead of behaviour chains
- ATT&CK and emulation planning are slower to operationalise
- useful behaviour context stays trapped in long-form reporting
Stixify helps make that behaviour more usable by turning report content into structured defensive context.
Use ATT&CK as a consistent analytic layer
ATT&CK is valuable because it gives teams a shared language for behaviour. The challenge is converting the behaviour described in reports into that language consistently enough to support real workflows.
Stixify helps by making ATT&CK-aligned outputs easier to generate from source reporting. That helps analysts and defenders:
- search for reporting by specific ATT&CK techniques
- compare reports using a common behavioural reference point
- connect external reporting to internal detection and coverage work
- move from a technique mention to a wider set of related reports and patterns
This matters because ATT&CK is often most useful when it becomes a pivot rather than a label.
Why Attack Flow style context matters
A list of ATT&CK techniques is helpful, but it is not always enough.
What defenders often need next is ordered behavioural context. They need to understand not only which techniques appeared, but how they were used together and what likely came before or after.
That is where Attack Flow style outputs matter. They make it easier to reason about progression, adjacency, and behavioural chains. This helps teams:
- hunt for related activity around an observed technique
- understand likely follow-on behaviours
- plan emulation more realistically
- evaluate detections in the context of broader intrusion paths
This is one of the most useful differences between simple ATT&CK tagging and more operational adversary modelling.
Support detection and coverage reviews
One practical use of ATT&CK-aligned reporting is identifying gaps in defensive coverage.
Teams often review ATT&CK coverage in theory, but the most useful validation comes from observed behaviour. Public reporting provides examples of how real adversaries combine techniques in real intrusions. When that reporting is structured, it becomes much easier to compare it against existing detections, telemetry, controls, and playbooks.
Stixify helps make that comparison faster and more repeatable by turning report content into structured behaviour data that defenders can work from directly.
Make hunting and emulation more actionable
Hunt planning and adversary emulation are both stronger when they start from realistic behaviour instead of disconnected references.
Structured ATT&CK and Attack Flow outputs help teams build more useful workflows around:
- ATT&CK-oriented threat hunting
- detection engineering
- purple teaming
- attack simulation and emulation planning
- investigative reasoning around likely technique progression
This is especially useful when defenders are working from incomplete evidence. Public reporting will never mirror an internal incident perfectly, but structured ATT&CK and Attack Flow data can still provide a strong model for what to investigate next.
Explore next
- Want the broader outcome view? See Improve Detection and Hunting with Structured Threat Intelligence.
- Want to enrich observables and techniques with more linked report context? See Enrich IoCs and TTPs from Unstructured Reporting.
- Want to feed the output into other systems? See Integrate Stixify into Your Security Stack and AI Workflows.
