Use Cases
Explore practical ways teams use Stixify for document processing, enrichment, ATT&CK analysis, investigation, and integrations.
Overview
Use-case pages are the best place to understand how Stixify supports a specific analyst workflow.
Each page below focuses on a concrete job: processing reports and documents, enriching IoCs and TTPs, mapping adversary behaviour to ATT&CK, accelerating investigations, or integrating structured intelligence into the rest of the stack.
Explore use cases
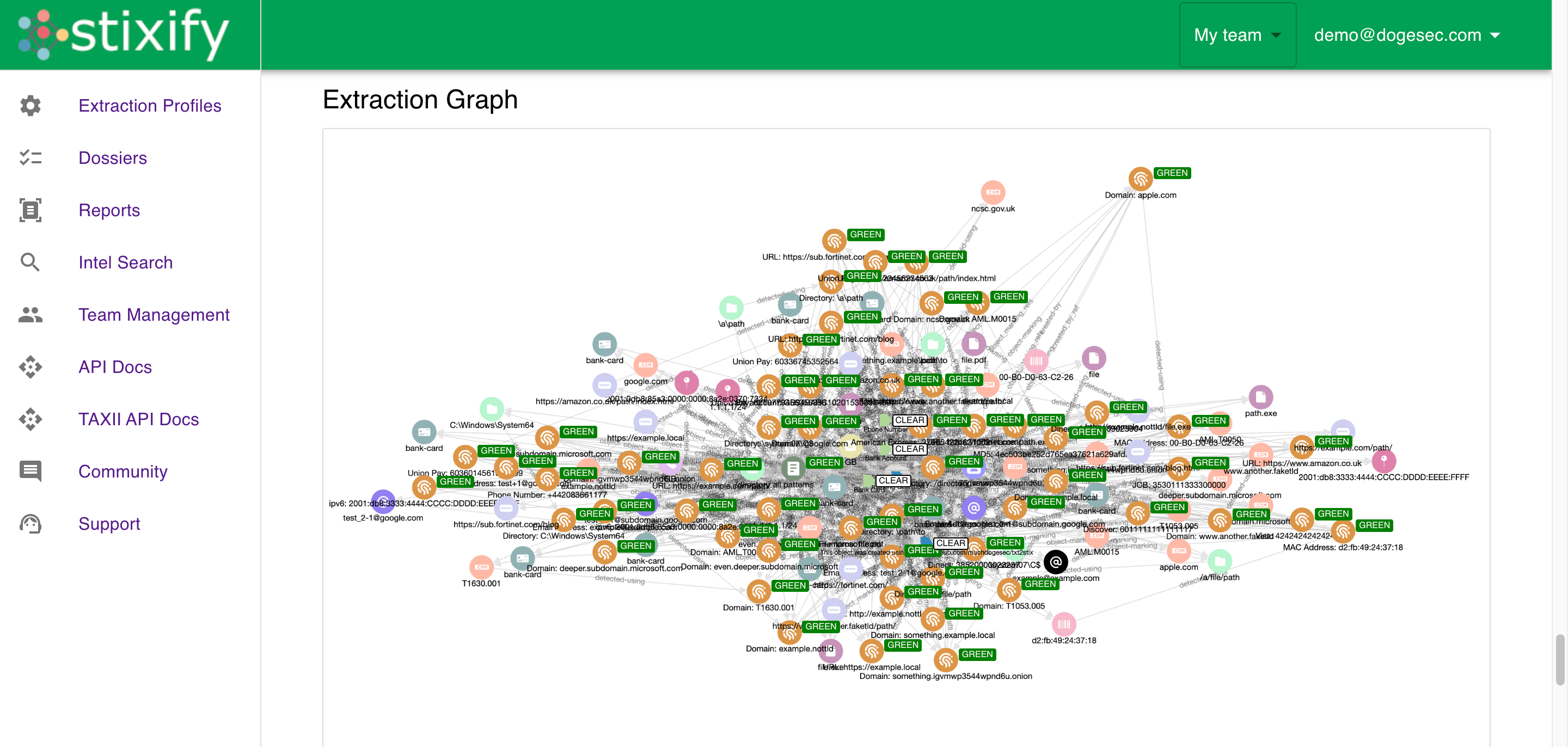
- Extract Threat Intelligence from Unstructured Documents: Turn PDFs, Word documents, slides, and pages into structured intelligence that can be reused.
- Enrich IoCs and TTPs from Unstructured Reporting: Start from an observable, technique, or report and build more context around it.
- Map Reports to MITRE ATT&CK and Attack Flow: Move from narrative reporting to ATT&CK-aligned techniques and ordered behaviours.
- Accelerate Threat Research and Investigation: Cross-reference faster, spot patterns, and keep investigations moving.
- Integrate Stixify into Your Security Stack and AI Workflows: Feed structured intelligence into other platforms, automations, and agent workflows.
Looking for outcomes instead?
If you want the broader team or business outcome rather than a specific workflow, start with the Solutions pages.
