Extract Threat Intelligence from Unstructured Documents
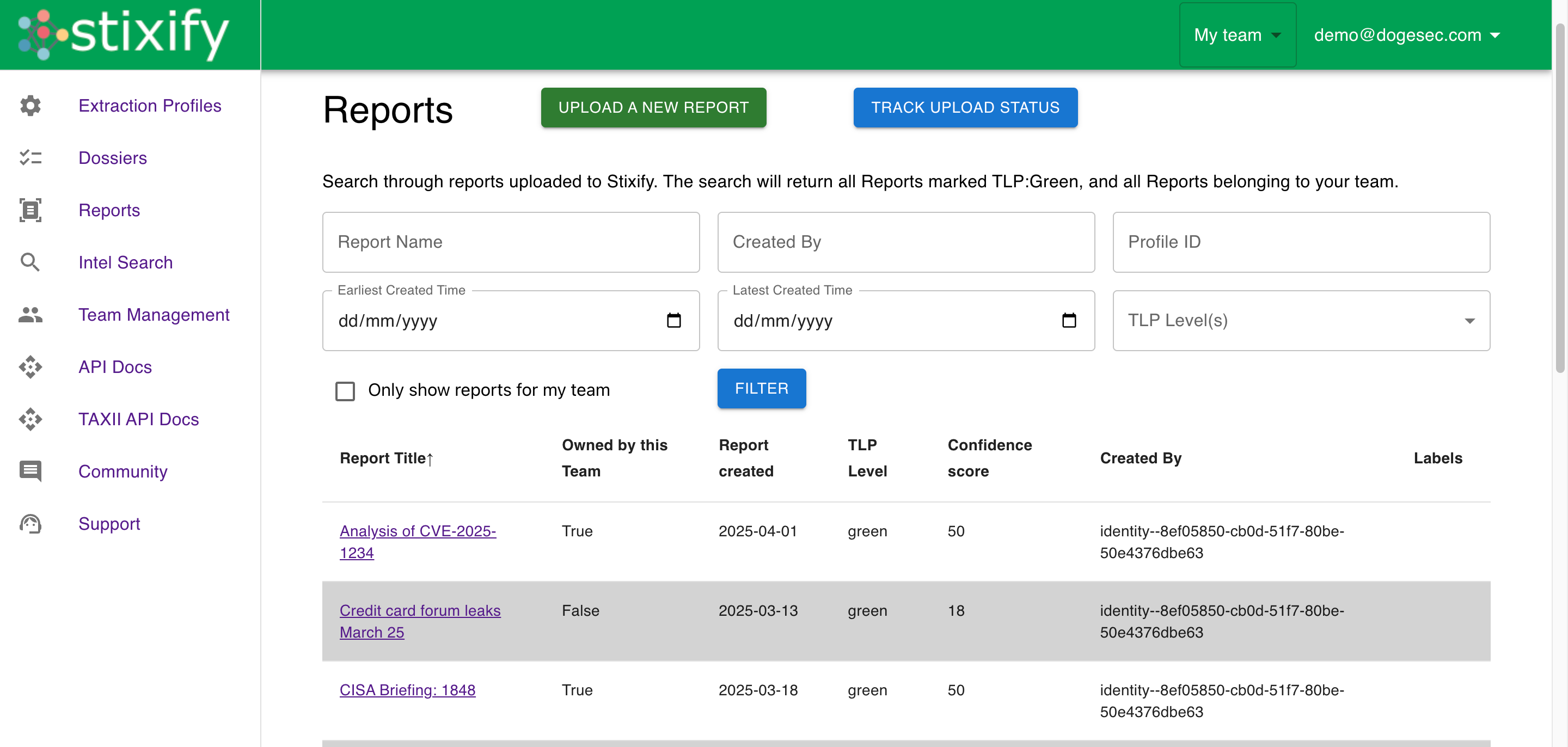
Use Stixify to turn PDFs, Word documents, slides, web pages, and similar source material into structured STIX 2.1 intelligence.
Overview
Many of the most useful threat reports are still shared in formats that are hard for downstream systems to use directly. PDFs, Word documents, slides, HTML pages, and similar source material often contain valuable observables and behaviour detail, but analysts still need to extract and normalise that information before it becomes operational.
Stixify helps teams process that material into structured STIX 2.1 intelligence so the value of a report can move beyond the document itself.
This is useful whether the source material comes from vendor reporting, community research, internal collections, customer submissions, or any other workflow where CTI content arrives as a document first and usable intelligence only later.
What this solves
Without a structured extraction workflow:
- reports stay trapped in manual reading queues
- analysts copy IoCs and TTPs out by hand
- relationships between observables and behaviour are easy to lose
- downstream tools cannot use the report without more manual processing
- later enrichment work starts from fragmented notes instead of structured objects
Stixify helps solve this by turning the source material into reusable intelligence instead of leaving it as narrative text.
Start with the report you already have
One of the strengths of this workflow is that it starts where teams already work.
There is no need to wait for a source to publish data in a structured format. Analysts can begin with the documents and pages they are already collecting and move directly into an extraction workflow that produces more operational outputs.
That is useful in practice because CTI often arrives unevenly:
- one report might be a PDF
- another might be a Word document
- another may only exist as an HTML page
- another may come from an internal upload or ad hoc submission
Stixify helps create a more consistent intelligence layer above that variability.
Preserve more than just indicators
A weak extraction workflow often stops at a list of indicators.
That can still be useful, but it leaves a lot of value behind. Reports also contain behavioural context, ATT&CK-aligned techniques, relationships between entities, and clues that make later analysis easier.
Stixify is more useful when it preserves those richer parts of the report as structured intelligence too. That helps teams avoid the common problem where an indicator is extracted, but the reason it mattered is lost.
Why this matters operationally
This use case matters because extraction is the entry point for everything else. If a report never becomes structured intelligence, it is much harder to enrich, correlate, share, or operationalise later.
Turning reports into structured STIX 2.1 data gives analysts and downstream systems a better foundation to work from. It also makes later workflows more repeatable because teams are not reconstructing the same basic context each time the report becomes relevant again.
Where this fits in the workflow
This use case is especially useful when teams need to:
- process a new report quickly
- extract IoCs and techniques into a usable format
- preserve linked context between the report and its extracted objects
- prepare intelligence for search, pivoting, and export
- reduce repetitive analyst effort across many similar documents
It is the natural starting point for most of the broader Stixify value story.
Explore next
- Want the broader outcome view? See Operationalise Threat Intelligence Extraction.
- Want to build more context around extracted observables and techniques? See Enrich IoCs and TTPs from Unstructured Reporting.
- Want to move the output into other systems? See STIX Bundle Export.
